
[ad_1]
The rapid shift to remote and hybrid working has led to growing concerns about digital security. Whether your team is fully office-based, fully remote, or somewhere in between, these threats mean your business must have safe Unified Communications.
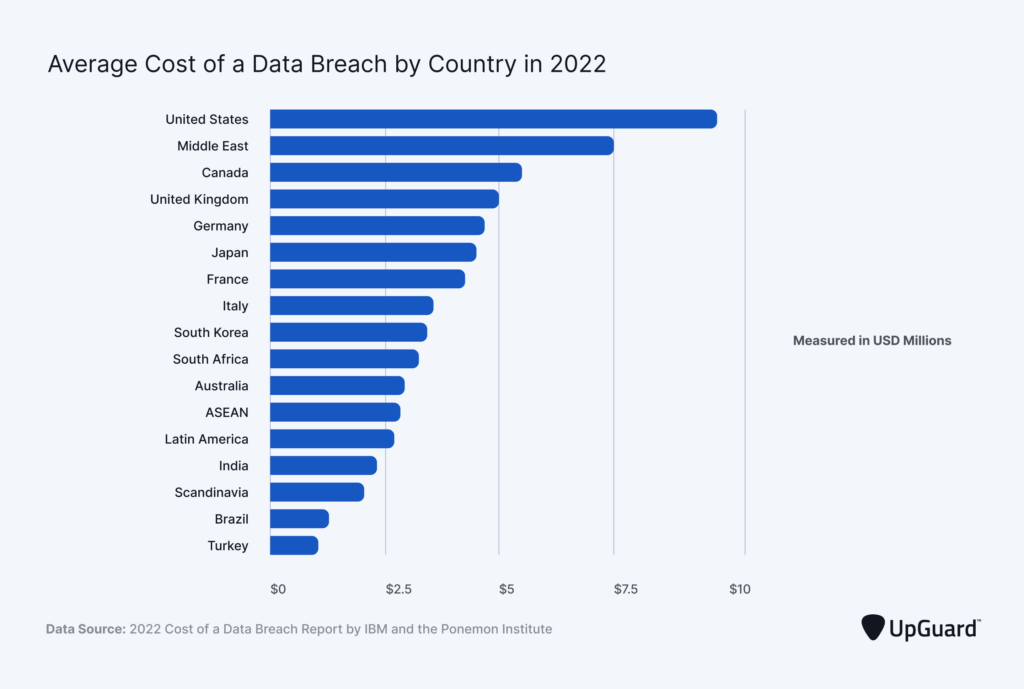
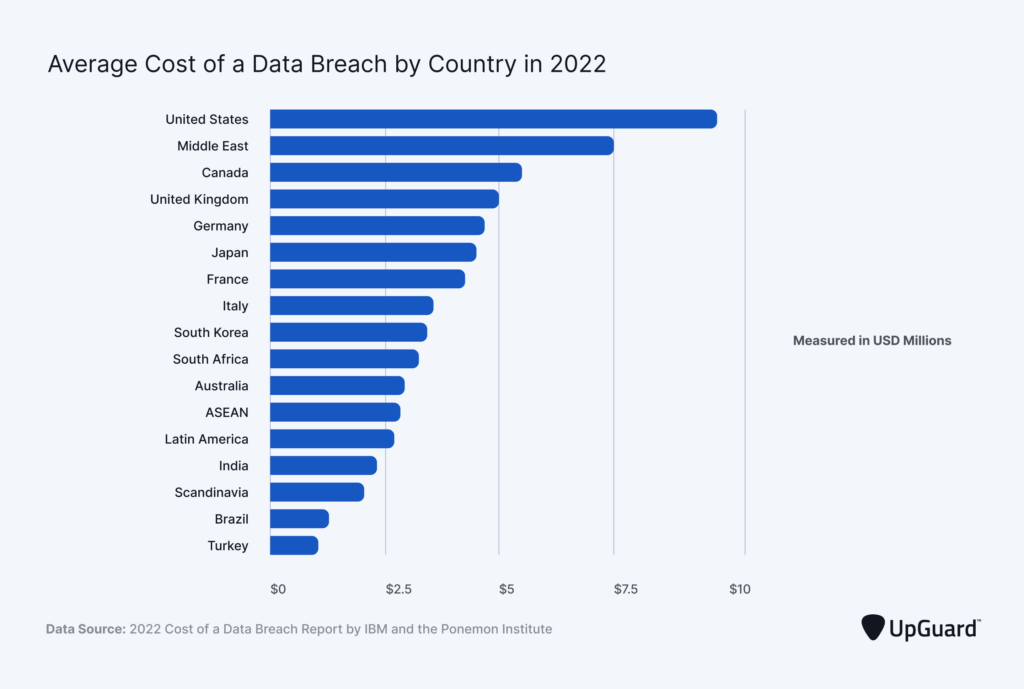
Any delay in securing communications can be costly. In fact, the average cost of a data breach continues to rise and is now $9.48 million Applicable to US companies.
Learn the four unified communications security threats you should be aware of and how to combat them.
Key Takeaways:
- Denial of service and theft of service attacks remain the greatest threat to digital communications.
- You should ensure that your providers and employees adhere to strict safety protocols.
- To ensure secure unified communications, you need a provider that can protect you across seven pillars.
Four major threats to unified communications security
Cyber attacks come in many forms. However, the most common forms of attacks fall into the following four categories.
1. Distributed Denial of Service Attack
A DDoS attack bombards your unified communications service with traffic, such as incoming messages or calls. Overload can result in poor call quality, lost connections, or even service outages.
Some attackers demand ransom, while others seek a competitive advantage. Other hackers use DDoS tactics to distract your security team while they conduct more sinister attacks, such as stealing confidential data.
2. Theft of Services
Modern scammers may try to hack into your phone service so that the authorities cannot trace the calls. As a result, you may have to prove that you are not the source of the scam calls. This wastes valuable time and can lead to legal problems.
3. User or system vulnerabilities
Security threats can come from within an organization. However, the problem is not necessarily employees trying to steal or misuse data for personal gain.
In many cases, poor access controls create vulnerabilities. Weak passwords or insecure devices can open the door for cyber attackers to gain access to a once-secure unified communications system.
your Communications Provider Does the system require regular password updates and multi-factor authentication?
More importantly, how secure are your provider’s data centers (physical and digital)? Lack of compliance or up-to-date defenses can compromise the security of your system.
4. New Phishing and Malware Techniques and Tools
Hackers are constantly coming up with new ways to do bad things. These people are often eager to share their latest techniques on the dark web.
Generally, these attacks come in the form of phishing or malware. malicious software A malware attack is a program that a user downloads to their system that sends confidential information back to the hacker. An employee might do this accidentally while conducting company business on an open Wi-Fi network.
Phishing This is when scammers try to get you to reveal private account information. This tactic is very different from the “foreign prince” email scam. For example, hackers can use artificial intelligence to imitate a voice you know and ask for sensitive account credentials to break into your system.


7 pillars of security and protection to eliminate threats to unified communications
The best way to combat threats and ensure unified communications security is to work with World-class supplier Security is handled for you. A worry-free platform with the following elements minimizes the impact of cyberattacks.
1. Comprehensive data security through access control and encryption
You need to rely on encrypted emails, files, videoconferenceand voice calls. Make sure your provider uses industry-standard protocols, such as TLS, SSL, and WebRTC, to prevent intruders from gaining access to your confidential information.
2. Server and client backup
No need to worry about losing data in the event of a power outage or unexpected emergency. Secure Unified Communications Provider Back up your data On servers in different locations. Likewise, your management portal should allow you to restore any past versions of your files or prevent permanent deletion by unauthorized parties.
3. Endpoint protection across devices
Email services require comprehensive spam, virus, and malware protection, and the ability to instantly receive the latest updates from the provider. Additionally, endpoint detection and response capabilities have processes in place to immediately respond to any suspicious activity on any type of device.
4. Identity Protection Protocol
Administrators must be able to selectively enable service permissions for end users. Password management should also be simple in the portal. Administrators can create policies to determine password strength and expiration.
5. Complete infrastructure security
Your provider should guarantee full physical and digital security of its data centers, including:
- Employee background checks and restricted server access
- 24/7 on-site security and CCTV
- Redundant ISPs with DDoS protection
Additionally, an independent source should verify that your claims of UC are truly secure.
6. Data Control and Privacy
Comprehensive data policies ensure that you conduct international business without violating compliance standards in key markets such as the US and EU. If a private cloud is necessary for customized security, for example, then this is another feature you should be able to request.
7. Continuous security management
Automated logs, advanced analytics, and real-time notifications help you and your provider quickly identify and resolve any threats. Behind the scenes, your vendor conducts penetration testing and code reviews to eliminate vulnerabilities.
Get a worry-free, secure unified communications platform
Intermedia ensures comprehensive protection of seven key pillars of data and physical security. register For more information about our secure unified communications-as-a-service platform or to get more information, please contact one of our agents for an immediate call back.
August 1, 2024
Explore other posts on these topics: Safety
[ad_2]
Source link


